Three months? Six months? Maybe a quick update sometime right before the last audit?
You’re not alone in this. It’s not a failure-it’s a structural problem. Most ISMS tools are compliance tools that assume infrastructure remains static. You set them up once, maintain them half-heartedly, and hope the auditor doesn’t dig too deep.
We built COD-ISMS because we face this reality every day. And because there’s a better way.
The real problem: two worlds that never come together
In every company, there are two parallel realities:
Reality 1: The infrastructure. IT systems, OT systems, medical devices, substations, production control systems. It is constantly changing. Devices come and go. Configurations change.
Reality 2: The ISMS. Asset lists, risk assessments, controls. Maintained by people, based on data from three months ago.
The gap between these two worlds is the blind spot of every traditional ISMS. And that is precisely where attackers strike—and auditors as well.
COD fills this gap. Automatically.
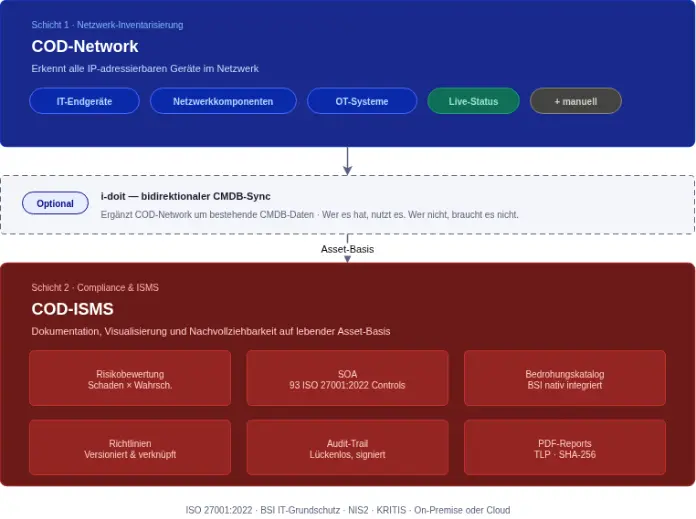
COD is an integrated platform consisting of various modules that work together seamlessly:
Layer 1: COD Network – Network Inventory as a Starting Point
COD-Network automatically detects all IP-addressable devices on the network—from IT endpoints and network components to OT systems and industrial equipment—provided they are accessible via the network. Network topology diagrams are generated and imported.
What COD-Network doesn't do yet: It doesn't automatically classify assets. The classification—what constitutes a firewall, a PLC, or a medical device—is done manually. To be honest, that makes sense: After all, anyone who knows their own infrastructure wants to make that decision themselves.
Layer 2: COD-ISMS – Structured Compliance Based on Real-Time Data
COD-ISMS uses the assets maintained in COD-Network as the foundation for a structured, documented ISMS.
What this means in concrete terms:
Manage controls, don’t just check them off. All 93 ISO 27001:2022 Annex A controls are included, grouped into four categories. For each control, you can record its applicability (yes/no), implementation status (implemented / partially implemented / planned / not implemented), notes, and linked policies. You can view your progress visually on the dashboard.
Policies that are truly part of compliance. Policies are directly linked to the corresponding controls—versioned, with a diff view, and featuring a seamless workflow from draft to archive.
An audit trail worthy of the name. Every change—to assets, controls, policies, or risk assessments—is fully logged. Who, when, what, where, why. Tamper-proof and server-signed. This forms the basis of traceability for external audits.
Risk assessments for the specific asset. Not for “network components in general,” but for the specific asset—using the live status provided by COD-Network.
An audit trail worthy of the name. Every change is fully logged. Who, when, what, where, why. Tamper-proof and server-signed.
On-premises or cloud—both options, full control
Especially in the KRITIS environment, “no data in the cloud” is often not a preference but a requirement. COD runs entirely on-premises—on your infrastructure, in your data center.
And yet: Template updates—new ISO controls, an updated BSI catalog, policy templates—are provided centrally and can be deployed in a controlled manner. No cloud requirement. No outdated content.
Who COD-ISMS was designed for
For IT managers who don’t have time to maintain asset lists manually—but still need a clean, well-documented ISMS foundation.
For CISOs who want to know: Which controls have been implemented and documented, and which ones are still pending? – and who want an answer based on a current asset inventory.
For executives operating in regulated environments who understand that an ISMS that does not reflect reality is not a safeguard—it is a matter of liability.
Conclusion: An ISMS that knows what it’s protecting—and honestly states what it can do
Most ISMS tools know what you told them—months ago. COD combines network inventory and compliance documentation in a single platform—without manual workarounds or duplicate data entry.
If you’d like to see exactly how this works in your area, we’d be happy to show you. We’ll give you a practical demonstration, with no sales pressure and no 47-page proposal required upfront.